The realm of cryptography has long fascinated individuals with its intricate methods of securing information. Among the various techniques employed, the transposition cipher stands out as a fundamental yet effective means of encrypting data. A transposition cipher works by rearranging the letters of the plaintext according to a specific pattern or key, rather than replacing them as in substitution ciphers. The complexity and security of these ciphers can vary greatly depending on the method used for transposition. For those looking to decipher messages encoded with such a cipher, a transposition cipher decoder tool is an indispensable asset.
Understanding Transposition Ciphers

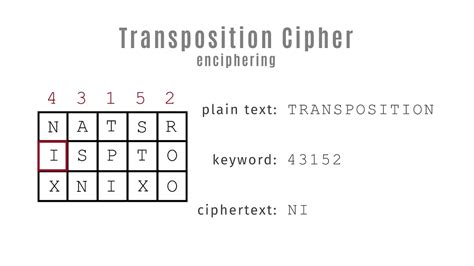
To effectively utilize a transposition cipher decoder tool, one must first grasp the basics of how transposition ciphers operate. These ciphers can be broadly categorized into two types: columnar transposition and row-column transposition, among others. The columnar transposition involves writing the plaintext in rows and then rearranging the columns according to a specific key. In contrast, the row-column transposition method involves a more complex process of rearranging both rows and columns. Understanding the type of transposition used is crucial for decoding the message.
Key Components of a Transposition Cipher
A transposition cipher decoder tool typically requires knowledge of the cipher’s key or pattern. This key determines how the plaintext is rearranged to form the ciphertext. Without the key, deciphering the message can be extremely challenging, though not impossible. Advanced decoder tools may employ algorithms to attempt to deduce the key through frequency analysis or other cryptographic techniques. However, for most practical purposes, having the key or being able to deduce it logically is essential for effective decoding.
| Type of Transposition Cipher | Description |
|---|---|
| Columnar Transposition | Involves rearranging the columns of the plaintext according to a specific key. |
| Row-Column Transposition | A more complex method involving the rearrangement of both rows and columns. |
Functionality of a Transposition Cipher Decoder Tool
A well-designed transposition cipher decoder tool should offer a user-friendly interface where one can input the ciphertext and any known parameters of the cipher, such as the key or the type of transposition used. The tool then applies algorithms to rearrange the ciphertext back into its original form, the plaintext. For more complex ciphers or when the key is unknown, the tool may offer options for brute force attacks or frequency analysis to attempt to crack the code.
Technological Implementation
The technological implementation of a transposition cipher decoder tool can vary, ranging from simple command-line tools to complex web applications. Modern tools often incorporate sophisticated algorithms and machine learning techniques to improve their effectiveness, especially in cases where the cipher’s specifics are unknown. For instance, a tool might use natural language processing to analyze the frequency of letters in the ciphertext to make educated guesses about the key.
Key Points
- The effectiveness of a transposition cipher decoder tool depends on the knowledge of the cipher's key or pattern.
- Understanding the type of transposition cipher used is crucial for decoding the message.
- Advanced tools may employ frequency analysis or machine learning to deduce the key when it is unknown.
- Transposition ciphers, while educational, are not considered secure for modern data protection.
- A well-designed decoder tool should offer a user-friendly interface and the capability to handle various types of transposition ciphers.
Conclusion and Future Directions
In conclusion, transposition cipher decoder tools are valuable resources for both educational purposes and historical cryptographic analysis. However, as cryptography continues to evolve, the focus has shifted towards more secure and complex encryption methods. The development of transposition cipher decoder tools, therefore, also evolves, incorporating more advanced technologies and algorithms to tackle the challenges posed by these ciphers. For those interested in cryptography, exploring transposition ciphers and their decoder tools can provide a fascinating glimpse into the history and development of encryption techniques.
What is the primary challenge in decoding a transposition cipher?
+The primary challenge is often determining the key or pattern used for the transposition. Without this information, decoding can become significantly more complex.
Are transposition ciphers still used today for secure communication?
+No, transposition ciphers are not considered secure enough for modern data protection. They are primarily used for educational purposes or in historical contexts.
How do transposition cipher decoder tools handle unknown keys?
+Decoder tools may use frequency analysis, brute force attacks, or machine learning algorithms to attempt to deduce the key and decode the message.